Twenty-seven percent of malware incidents reported in 2020 can be attributed to ransomware.
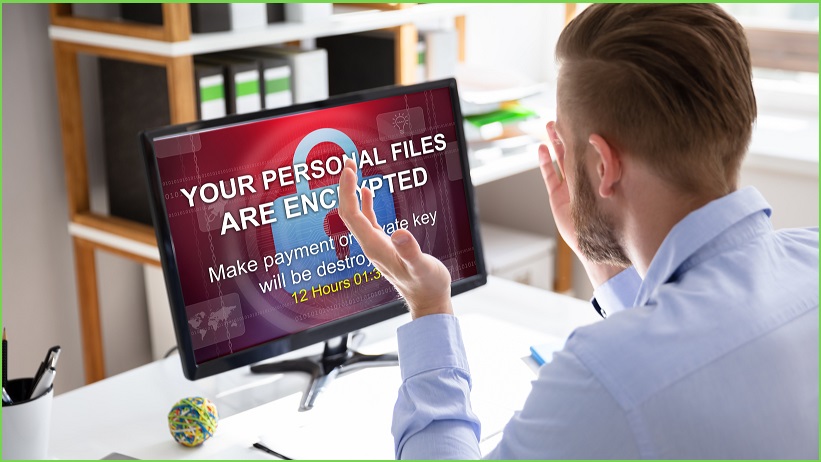
Ransomware — cyber extortion that occurs when malicious software infiltrates computer systems and encrypts data, holding it hostage until the victim pays a ransom — can have a bigger impact on an organisation than a data breach.
In the short term, ransomware can cost companies millions of dollars, and a potentially even greater loss over the long term, impacting reputation and reliability.
From top healthcare providers and retailers in the US to insurance providers in the Middle East, ransomware attackers are proving to be a continuing cybersecurity threat.
Organisations need to focus on is preparation and early mitigation if they want to cut losses.
“In some recent cases of ransomware attacks, the victim organisations have paid huge amounts to the attackers, which can be one of the reasons these attacks are getting more popular,” says Paul Webber, Senior Director Analyst, Gartner.
“Instead, what organisations need to focus on is preparation and early mitigation if they want to cut losses to ransomware.”
CISOs and security leaders can reduce the likelihood of ransomware attacks, reduce exposure to vulnerabilities and secure the organisation using a mitigation plan.
This plan must cover the following six actions.
#1: Conduct initial ransomware assessments
Conduct risk assessments and penetration tests to determine the attack surface and current state of security resilience and preparedness in terms of tools, processes and skills to defend against attacks.
“Before you assume that payment is the only option, investigate using free ransomware decryption software,” says Webber.
#2: Enforce ransomware governance
Establish processes and compliance procedures that involve key decision makers in the organisation, even before preparing for the technical response to a ransomware attack.
Ransomware can escalate from an issue to a crisis in no time, costing an organisation revenue loss and creating a damaged reputation.
Key people such as the CEO, board of directors and other important stakeholders must be involved in the preparation.
In the event of a ransomware attack, it is likely that journalists and other external stakeholders will reach out to the board of directors for response to the attack, not the security leaders or CISO.
#3: Maintain consistent operational readiness
Conduct frequent exercises and drills to ensure that systems are always able to detect ransomware attacks.
Build regular testing of incident response scenarios into the ransomware response plan.
Test, test and retest at regular intervals to check for vulnerabilities, non-compliant systems and misconfigurations.
Ensure that incident response processes are not themselves reliant on IT systems that may be affected by ransomware attacks or unavailable in case of a serious incident.
#4: Back up, test, repeat ransomware response
Back up not only the data but also every non-standard application and its supporting IT infrastructure.
Maintain frequent and reliable backup and recovery capabilities.
If online backups are used, ensure that they cannot become encrypted by ransomware.
Harden the components of enterprise backup and recovery infrastructure against attacks by routinely examining backup application, storage and network access and comparing this against expected or baseline activity.
Prepare for critical application recovery in a systemwide ransomware attack by creating specific recovery time objective (RTO) and recovery point objective (RPO) parameters, safeguarding backup storage media and accessibility.
#5: Implement the principle of least privilege
Restrict permissions and deny unauthorised access to devices.
Remove local administrator rights from end users and block application installation by standard users, replacing this with a centrally managed software distribution facility.
CISOs and security leaders must deploy multifactor authentication wherever possible, especially for privileged accounts.
Increase authentication logging on all critical servers, network appliances and directory services, and ensure logs are not deleted.
Notify security operations teams of any unexpected activity and ensure they proactively look for unusual logins/failed authentication attempts.
# 6: Educate and train users on ransomware response actions
Research government and regional authorities that have provided guidelines on how organisations can fortify their network infrastructure against ransomware.
CISOs and security leaders can use guidelines such as these to create a basic training program for all staff in the organisation.
However, ransomware preparedness training needs to be customised to the organisation for better results.
“Use cyber crisis simulation tools for mock drills and training that provide closer to real-life situations for better preparedness of end users against ransomware,” says Webber.
The challenges of ransomware and other forms of malware are the ever-changing tactics and agendas of hackers.
Having a strategy in place for preparedness can help contain the losses and protect the organisation.
This article was originally published by Gartner.