Medibank customers are bracing themselves for the worst after the private health insurer refused to pay a ransom for stolen customer data, leading the alleged hacker to proclaim the data would be published online within 24 hours.
The health insurer's ongoing investigations have revealed much more data was accessed than previously thought, including some health claims data and the names, addresses, dates of birth, phone numbers, and email addresses for some 9.7 million current and former customers.
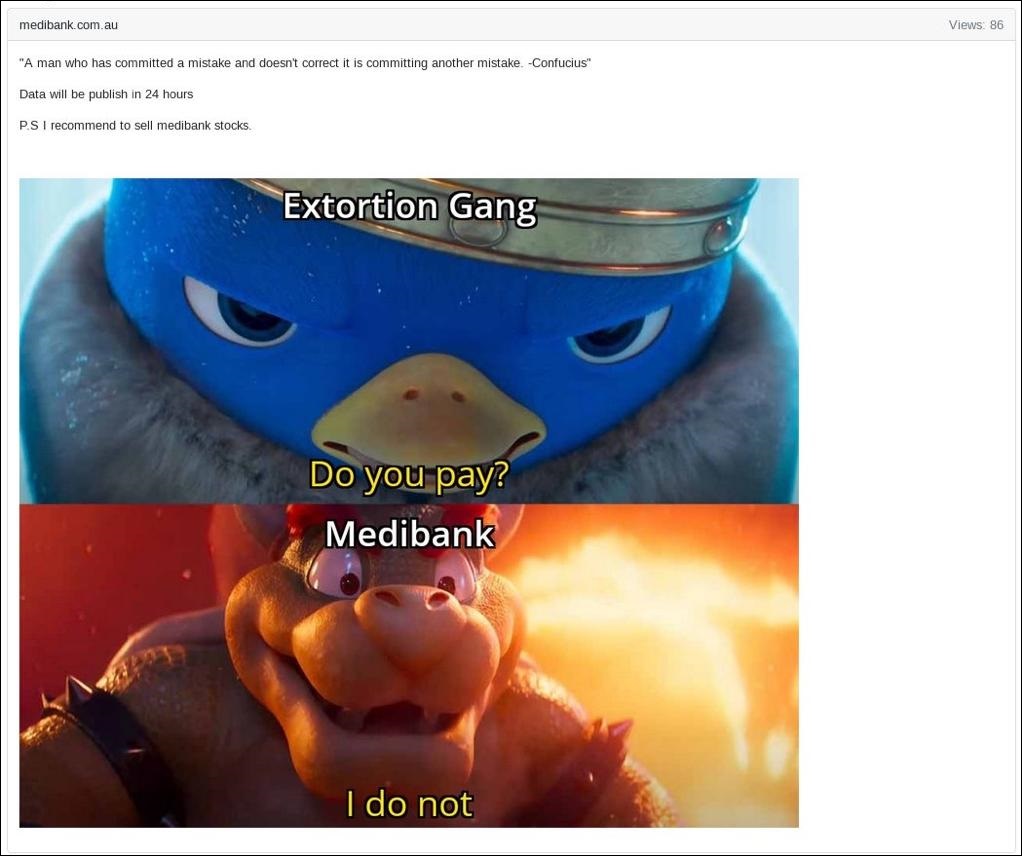
The alarming announcement arrived in the form of a bizarre post to a dark web forum – containing a quote from Chinese philosopher Confucius, a Super Mario Bros meme, and a flippant, 24-hour warning for what could be one of Australia's largest ever data leaks.
The post opened with a foreboding Confucius quote, reading: 'A man who has committed a mistake and doesn't correct it is committing another mistake.'
Under this, the post added "Data will be publish in 24 hours. P.S I recommend to sell Medibank stocks".
The self-proclaimed 'extortion gang' finalised the post with the following image:
The alleged hacker is yet to publicly substantiate its claims of stolen data, but earlier sent a sample of the stolen data to Medibank to verify its authenticity.
What data has been accessed?
Medibank discovered the attack on 12 October when it detected some 'unusual activity' on its network, initially finding no evidence of sensitive customer data having left its systems.
In the days that followed, however, Medibank gradually realised more and more customer data had been accessed, and eventually conceded the attacker had access to the data of all Medibank customers during the incident – meaning at least 4 million customers had been exposed to the attack.
Now, almost a month after the initial report, this figure has more than doubled, as Medibank now believes around 9.7 million current and former customers as well as some of their authorised representatives had their data accessed by the criminal.
"This figure represents around 5.1 million Medibank customers, around 2.8 million ahm customers and around 1.8 million international customers," said Medibank.
Medibank also believes the criminal "accessed Medicare numbers (but not expiry dates) for ahm customers", "accessed passport numbers (but not expiry dates) and visa details for international student customers", and "accessed health claims data for around 160,000 Medibank customers, around 300,000 ahm customers and around 20,000 international customers".
The health claims data reportedly impacted by this incident includes service provider name and location, the place where customer received medical services, the codes associated with diagnosis, and the procedures administered.
Furthermore, Medibank also discovered a smaller, but sensitive, subset of data belonging to customers of the at-home care service My Home Hospital had been accessed.
Strong stance on ransom demands
In addition to unveiling the gargantuan amount of data impacted to date, Medibank also announced its intentions surrounding any potential ransom demands for the attack.
"No ransom payment will be made to the criminal responsible for this data theft," said Medibank CEO David Koczkar. He explained the decision to forego ransom payouts, citing "extensive advice" the company received from cyber crime experts.
"We believe there is only a limited chance paying a ransom would ensure the return of our customers’ data and prevent it from being published," said Koczkar.
"In fact, paying could have the opposite effect and encourage the criminal to directly extort our customers, and there is a strong chance that paying puts more people in harm’s way by making Australia a bigger target.”
The decision is backed by conventional advice surrounding ransom events, with many cyber security experts agreeing that the act of paying a ransom often creates more problems than it aims to fix.
"Medibank’s decision to not pay the ransom is the smartest decision in this situation," said cyber security company Sophos’s Managing Director of ANZ, John Donovan.
"Pressure to retain customer and organisation data makes paying the ransom tempting, especially when the attack is as heavily publicised as Medibank’s, however companies rarely successfully recover by paying the ransoms," he said.
"The chance an organisation receives all its data back is minimal, and it can encourage criminals to retarget the same organisation, directly extort customers of that organisation, and on a macro level, make Australia a bigger target as criminals will see Australian organisations are willing to pay to retrieve stolen data," Donovan added.
Other sources, however, say the issue is more complex.
UNSW's Professor Lyria Bennett Moses told the ABC that Medibank was caught "between a rock and a hard place", adding there is "no right answer" regarding Medibank's approach to a potential ransom payout.
"On the other hand, by not paying the ransom, they increased the risk that individuals whose data is caught up in this, who obviously have done nothing wrong, will be directly harmed," said Moses.
Medibank said its decision is consistent with the position of the Australian Government – a statement which was later confirmed by Cyber Security Minister Clare O'Neil.
"Medibank’s decision is consistent with Australian government advice. Cyber criminals cheat, lie and steal," said O'Neil.
"Paying them only fuels the ransomware business model. They commit to undertaking actions in return for payment, but so often re-victimise companies and individuals," she added.
What's next for Medibank and its customers?
The Medibank attack now rival's Optus' recent landmark data breach in regards to the amount of data exposed.
Customers of Medibank are being cautioned to brace for the potential ramifications of this attack, which could include exposure of personal information, unwarranted contact from cyber criminals, and even personalised scams.
"Customers should remain vigilant as the criminal may publish customer data online or attempt to contact customers directly," said Medibank, less than a day before the hacker threatened to publish stolen data.
Medibank says it will continue to inform affected customers of which data has been accessed or stolen, as well as provide advice on what they should do.
Furthermore, Medibank has expanded its Cyber Response Support Program to include a cybercrime health and wellbeing phone line, a mental health outreach service for customers identified as being vulnerable, and additions to its Better Minds app for tailored preventative health advice and cybercrime resources.
“We take seriously our responsibility to safeguard our customers. The weaponisation of their private information in an effort to extort payment is malicious, and it is an attack on the most vulnerable members of our community,” said Koczkar.
Koczkar also announced Medibank will commission an external review to "ensure that we learn from this event and continue to strengthen our ability to safeguard our customers".
"To every person affected by this cybercrime I apologise unreservedly. The weaponisation of people’s personal data and health data in an effort to extort payment is sickening," he said.









