Education technology firm Instructure says it has reached an agreement with hackers after its popular learning platform Canvas suffered a data breach that potentially exposed details of up to 275 million students at around 9,000 institutions worldwide.
The US-based company announced “an agreement with the unauthorised actor” on Tuesday (AEDT), in which its stolen data had supposedly been returned.
Instructure has not confirmed if it paid a ransom to cyber extortion group ShinyHunters, which claimed responsibility for the attack, and did not name any specific cybercrime group.
The firm said it had “received digital confirmation of data destruction” by the hackers who targeted it, but concerns remain that the information could be used for attempted scams against students and educational staff.
ShinyHunters had set a final deadline of 12 May to be contacted for payment negotiations, and had threatened to publish its full dataset – supposedly totaling 3.65 terabytes – which Instructure said included information such as names, email addresses, and messages.
The company said hackers had agreed that “no Instructure customers will be extorted as a result of this incident, publicly or otherwise”.
“This agreement covers all impacted Instructure customers, and there is no need for individual customers to attempt to engage with the unauthorised actor,” the firm said in a statement.
“While there is never complete certainty when dealing with cybercriminals, we believe it was important to take every step within our control to give customers additional peace of mind, to the extent possible.”
Mohiuddin Ahmed, an associate professor in cybersecurity at Adelaide University, told Information Age that paying a ransom “is an extremely difficult decision for any victim”.
“However, it offers no guarantee that stolen data will be protected,” he said.
“In many cases, it only reinforces the attackers’ confidence and encourages further criminal activity.”
Dr Abu Barkat Ullah, an associate professor of cybersecurity at the University of Canberra, added that “even where agreements or payments occur, there is generally no absolute technical guarantee that exfiltrated data has been permanently deleted or will not later reappear through redistribution or secondary criminal marketplaces”.
Instructure details hackers’ ‘unauthorised activity’
Prior to announcing its “agreement” with the hackers, Instructure confirmed it had detected “unauthorised activity” in Canvas on two recent occasions, which it believed led to the data breach.
The first was on 29 April, claimed the company, which said it “immediately revoked the unauthorised party’s access, started an investigation, and engaged outside forensic experts”.
The second was on 7 May, when there was “additional unauthorised activity tied to the same incident”, the firm said.
“The unauthorised actor made changes to the pages that appeared when some students and teachers were logged in through Canvas,” the company said.
“Out of caution, we temporarily took Canvas offline into maintenance mode to contain the activity, investigate, and apply additional safeguards.”
Instructure said it had since confirmed “an issue” with support tickets in its ‘Free-For-Teacher' accounts had been exploited by the hackers on both occasions, which led the company to temporarily shut down those accounts.
Canvas is now "fully back online and available for use”, Instructure announced on Sunday (AEDT).
“Our external forensic partner has reviewed the known indicators and found no evidence that the threat actor currently has access to the platform," it said.
The company added that it was continuing to work with experts, including cybersecurity giant CrowdStrike, to strengthen its security and review the breach.
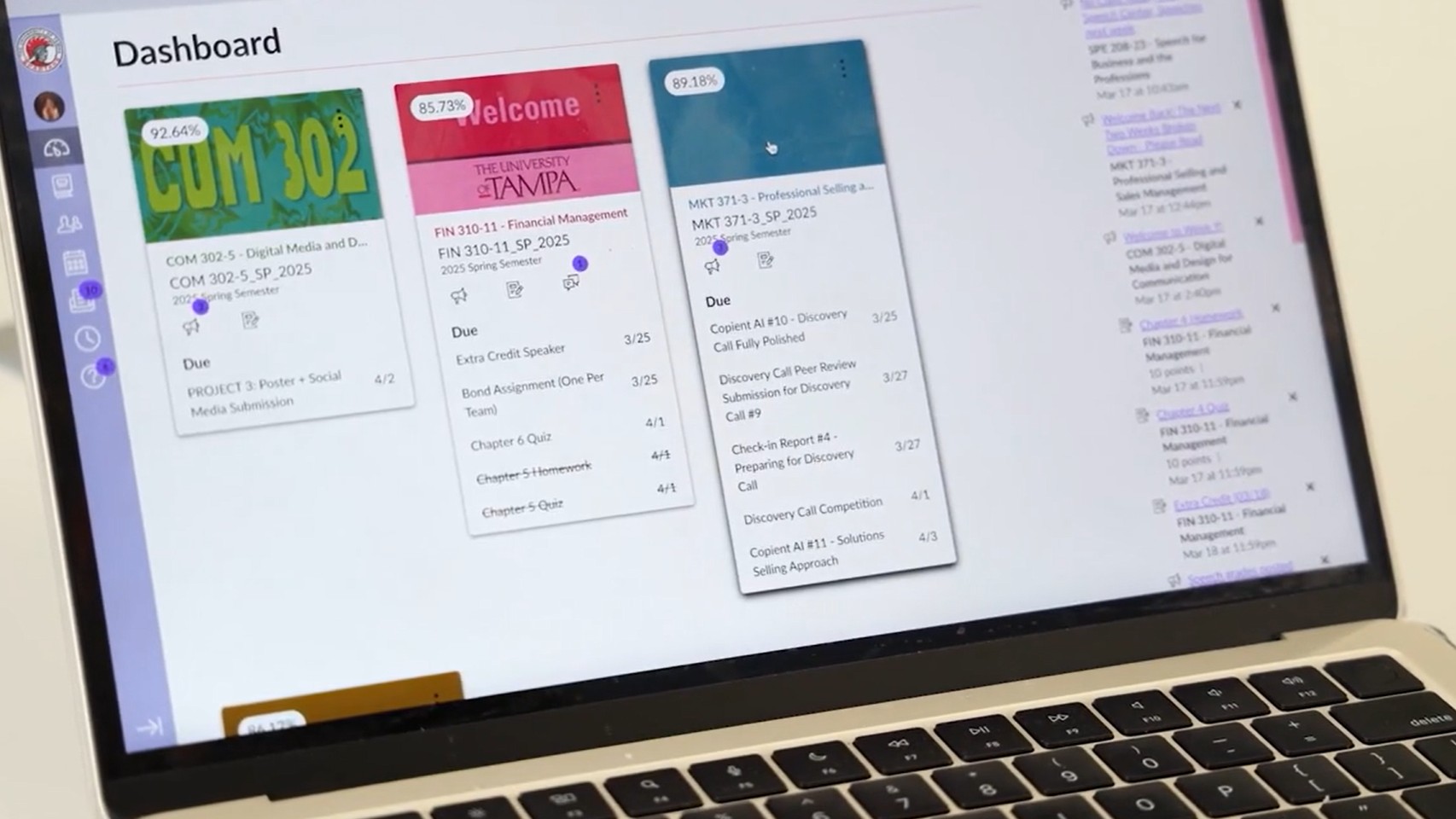
Canvas is a learning management system (LMS) developed by American company Instructure. Image: Instructure video
The incident is the second Instructure breached claimed by ShinyHunters in the past year, after the hacking group said it gained access to the company's Salesforce environment in September 2025.
Darren Guccione, CEO and cofounder of cybersecurity firm Keeper Security, said, “Two confirmed breaches by the same threat actor on the same platform suggests a pattern that demands scrutiny of whether remediation following the first incident went far enough.”
Guccione said ShinyHunters is pursuing “high-value” targets like Canvas with “increasing frequency”.
“Educational platforms hold an unusual concentration of sensitive data, such as personal identifiers, institutional records and private communications, making this a particularly consequential exposure,” he said.
Instructure said, “The prior Salesforce-related incident and this Canvas security incident are distinct events involving different systems and circumstances.”
Company CEO Steve Daly has apologised for the Canvas incident.
Associate professor Ahmed said hackers are “increasingly targeting companies with a global customer base and the financial capacity to pay large ransoms”, in a tactic known as ‘Big Game Hunting’.
“As a result, companies with international operations have become prime targets for these attacks.”
Some Australian institutions still wary of Canvas
Numerous Australian universities and schools have confirmed their staff and students have regained access to Canvas, but many have warned users to be wary of a potential increase in scam emails and phone calls.
Other organisations have been more cautious and decided not to allow access while Instructure continues to test and update its systems.
National cybersecurity coordinator Lieutenant General Michelle McGuinness said on Monday that “some Australian providers continue to use caution with regard to the security of the environment prior to re-enabling their Canvas instances”.
She said Instructure updated education sector stakeholders during a briefing held by the National Office of Cyber Security on Monday.
“Instructure advised it has undertaken a broad range of activities to ensure the Canvas environment is secure,” McGuinness said in a statement.
“… It will take time to understand the full impacts of any data exfiltrated as part of this incident.”
Instructure said it would notify individual institutions when it has verified “the identities of affected individuals" from each organisation “and the specific data impacted”.
The company previously said it “found no evidence” that passwords, dates of birth, government identifiers, or financial information had been compromised.
Australians warned of ‘elevated risk of scams’
McGuinness added that, “Consistent with other significant cyber incidents, there is an elevated risk of scams and phishing activity targeting students and staff, including attempts that appear to come from institutions, IT helpdesks or government.”
She said Australians “should be cautious, scrutinise unexpected contacts, avoid clicking suspicious links, and never share credentials or personal information unless they have verified the request through trusted channels".
“Institutions should reinforce these messages, provide guidance on recognising scams, and encourage prompt reporting of suspicious activity to local IT or security teams,” she added.
The Office of the Australian Information Commissioner (OAIC) said affected users wishing to make a privacy complaint against Instructure or an institution impacted by the data breach “must first lodge a complaint directly with Instructure or that entity” and allow at least 30 days for a response.
After this time, and “should the need arise”, the OAIC said its website provides guidance for those wishing to lodge a privacy complaint with its office related to Instructure or an affected entity.
While some educational institutions are covered by the Privacy Act, the OAIC notes that, “State and territory government schools are usually governed by state privacy laws, and public universities and TAFEs are generally exempt unless they operate as private entities.”










