Australian organisations are being urged to take caution after the systems of a US hospital equipment supplier were allegedly knocked offline by a pro-Iran hacking group.
Multinational medical and surgical equipment company Stryker announced Wednesday it was “experiencing a global network disruption” to an internal Microsoft environment as a result of a cyberattack.
In the days that followed, the Fortune 500 company headquartered in Kalamazoo, Michigan in the US worked to assess the full impact of the attack while customers faced “disruptions to order processing, manufacturing and shipping”.
A pro-Iran hacktivist group known as ‘Handala’ later claimed responsibility, saying the attack was retaliation for an alleged US Tomahawk missile strike on the Shajereh Tayyebeh Elementary School in Minab, Iran.
Information Age understands Stryker was last year awarded an ongoing US$450 million contract to supply medical equipment to the US military, including patient monitoring systems.
Although Stryker said its products were not affected, Handala claimed “over 200,000 systems, servers, and mobile devices” had been wiped and “50 terabytes of critical data” extracted.
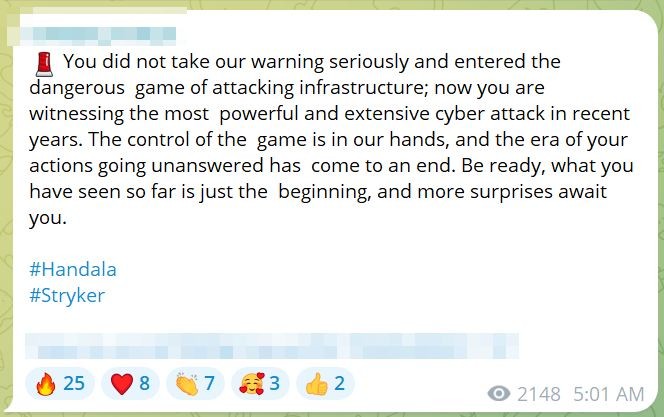
Handala celebrates its US hack and warns more attacks to come. Source: Telegram
Stryker has not verified those claims, but confirmed it was still working to restore its systems at the time of writing.
“Our core transactional systems are already on a clear path to full recovery, and we will continue to provide updates as progress is made,” the company told customers over the weekend.
Health officials in Victoria and NSW reportedly told the ABC there had been no observable disruptions as of Friday.
What cyber war risks could mean for Australia
As the federal government faces mounting pressure to clarify whether Australia is at war with Iran, cybersecurity experts have warned further attacks on US targets could create supply-chain impacts or other risks for Australian organisations.
In Stryker’s case, ABC reported hackers compromised the company’s deployment of device management platform Microsoft Intune, enabling them to remotely wipe devices worldwide.
The platform is widely used across Australian organisations to manage and secure devices, applications and corporate data, while Stryker’s medical equipment is used in hospitals across the country.
A spokesperson for the Australian Signals Directorate (ASD) told Information Age that, as noted in its Annual Cyber Threat Report 2024-25, geopolitical events “continue to challenge Australia’s security, including in the cyberspace”.
Speaking at the Gartner Security and Risk Management Summit on Monday, Australian Cyber Security Centre head Stephanie Crowe said the latest Middle East tensions could eventually have ramifications for Australian organisations.
“Right now, we don’t see the threat to Australian organisations [being] any different than it was a month or two ago,” said Crowe.
“But we could get caught up in collateral if we aren’t taking the steps that we should be doing on a daily basis to defend our systems and protect our networks.”

Stryker continues to investigate the attack on its systems. Photo: Shutterstock
Vaughan Shanks, chief executive of Melbourne-based incident response vendor Cydarm Technologies, said Iran’s targeting of US partners meant Australian critical infrastructure organisations should prepare for possible “opportunistic attacks” by groups linked to the Islamic Revolutionary Guard Corps (IRGC).
“Although Australia is a second-tier target behind the USA and Israel, the Iranian regime has form for attacking targets in Australia,” Shanks told Information Age.
“As a result, the IRGC has been declared a state sponsor of terrorism.”
Shanks described the conflict and related cyberattacks are a “wake-up call for critical infrastructure”.
“Nation state actors will seek to impose costs on their adversaries via destructive attacks on critical infrastructure,” he said.
“But the bigger risk is from cyber espionage – revealing intentions, plans, and capabilities of an adversary, and identifying targets for possible future kinetic action.”
Handala’s primary target
Handala has operated since at least 2023 and is widely believed to have links to Iran’s Ministry of Intelligence and the IRGC.
While the group framed the Stryker attack as retaliation for the alleged strike on the Iranian school, Shanks said the likely goal was psychological warfare.
“The more likely strategy is to demonstrate that the IRGC can strike anywhere in the world,” he said.
Handala has most frequently targeted Israel, claiming attacks against a range of organisations and infrastructure linked to the country’s military operations in Palestine.
According to Wired, however, several Israeli cybersecurity experts believe the group could be a front for Iran’s Ministry of Intelligence.
The group has also claimed attacks on organisations in the US, UK and Canada that it perceives as allied with Israel.
Meanwhile, Prime Minister Anthony Albanese announced last week Australia would deploy 85 personnel and a military aircraft to the United Arab Emirates to help defend the region.
Cybersecurity minister Tony Burke did not respond prior to publication when asked whether Australian organisations should be cautious about the possibility of war-related cyberattacks.










