Strong support from incubators and cybersecurity industry-development funding have helped Australian startup HackHunter bring its rogue WiFi network finder to market after a more than two-year R&D effort that could take the company to the US by next year.
Early trials of the HackHunter Pursuit, a portable Internet of Things (IoT) device, proved that the WiFi sniffer could not only detect WiFi signals, but trace them back to their source with centimetre accuracy.
The technology is designed to help companies identify and locate potential rogue WiFi access points, which have been deployed in public settings to steal user credentials and data.
Given how easy it is to set up WiFi access points – most modern smartphones can set up anywhere with the touch of a button – the threat has expanded in recent years.
Malicious WiFi ‘pineapples’, which interject themselves into a target network, are favoured tools of hackers and penetration testers who use a range of applications to intercept and steal data.
Validation shows market potential
Early technology trials within an ASX 50-listed company found a WiFi device hidden under the floor, while another WiFi signal was traced to a bag but switched off as investigators neared the source.
The HackHunter device is about more than just finding the networks, however: thanks to the integration of packet-sniffing and analysis technology as an “engine on a chip”, CEO Tracie Thompson told Information Age, the unit can also determine which WiFi hacking applications the attacker is attempting to use.
“We look at the disassociation packets and deauthentication packets and the ratios, and from that we can tell what is happening, and what tool is doing it,” she explained.
“Some tools have specific ratios that they use, and we have investigated those to find out their signatures. We can look at the entire network’s traffic, and look specifically at the behaviour on the network.”
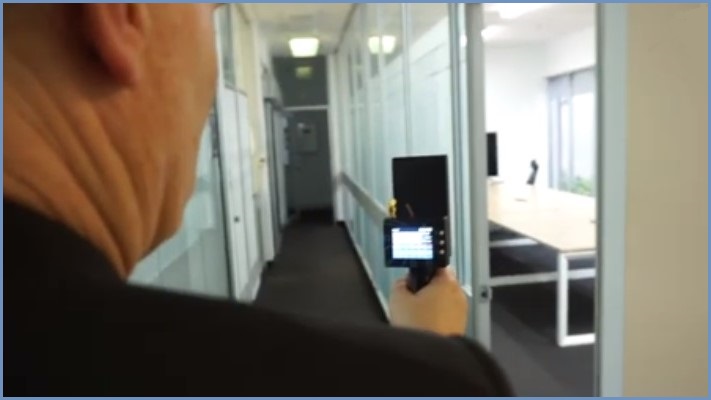
The 3D-printed, Australian-made Pursuit device has now been launched as a handheld unit that weighs less than 250g, runs for over 10 hours on a charge, and can be used and operated in just one hand.
“Red teams and penetration testers are expected to do WiFi audits but they don’t have the tools to do them,” Thompson said. “When we talk with pen testers about this, their eyes light up.”
Validation testing showed that its compact design makes it far easier to use than conventional jerry-rigged solutions that often combine laptops running custom scripts and WiFi sniffers, bulk directional antennas and power-hungry equipment that can require two people just to locate a WiFi signal.
“We were finding the WiFi devices before they could, and they couldn’t tell us anything about the devices – whereas we could tell them details about the hotspot before we even found it.”

HackHunter sniffs out dodgy access points. Photo: Supplied
The road to the cutting edge
As a small startup – Thompson and co-founder husband Mike Thompson have just a handful of employees providing technical and business development capabilities – HackHunter has drawn extensively on the evolving support ecosystem designed to help Australian cybersecurity innovators commercialise their ideas.
Recognised by peak industry body the Australian Information Security Association (AISA) as Cyber Security Start Up of the Year, HackHunter was an early participant in the Startmate and CyRise accelerators, whose support and networking opportunities helped the team refine its ideas.
The incubators also provided introductions to dozens of CISOs who offered their thoughts on the product’s design and potential value to penetration testers and other security professionals.
While it’s not yet a consumer-level device, Thompson believes the device will find a broader role as customers explore its capabilities in other use cases – for example, in detecting the WiFi signals being used to fly inexpensive drones that deliver contraband over prison walls.
Another potential use is to detect WiFi-operated cameras hidden in hotels or AirBnB rentals, where unscrupulous operators have been found secretly recording guests and posting their footage online.
Having secured $535,060 in funding during the second round of the AustCyber Projects Fund, the company is expanding its threat analytics capabilities and has its eyes on the US market.
After successful trials with a “large defence company” in that country paved the way for the company to start selling Pursuit in that country by next year, Thompson said, the biggest market for Pursuit “will probably be the US – but we see it as being totally global.”