Wearable tech and GPS navigation company Garmin went offline on Friday, locking its users out from updating their physical activity statistics as the result of what some reports suggest is a devastating ransomware attack.
In a statement, Garmin said it was “experiencing an outage” that affected the website and mobile app which people use to sync data from wearable devices to Garmin’s cloud servers.
“This outage also affects our call centres, and we are currently unable to receive any calls, emails or online chats,” Garmin said.
The warning that Garmin’s outage extended beyond its web servers suggested the problem was more widespread than it initially appeared.
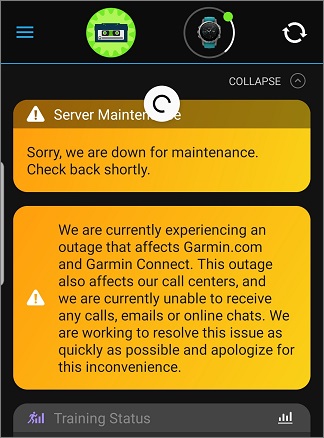
A screenshot from a Garmin watch warning that servers were down.
Along with personal fitness tracking and GPS, Garmin also provides navigation services for aviation.
Sources told Taiwanese news outlet iThome that Garmin’s Taiwanese IT department sent notice to Taiwanese authorities about an attack on their systems and that it would be shutting down local production.
ZDNet also reported that Garmin employees referred to the incident online as a ransomware attack – specifically naming the new WastedLocker ransomware.
Garmin has not yet confirmed whether its massive outage was caused by ransomware or any such cyber attack.
Severe, widespread business disruptions are consistent with ransomware attacks.
This outage also affects our call centers, and we are currently unable to receive any calls, emails or online chats. We are working to resolve this issue as quickly as possible and apologize for this inconvenience. (2/2)
— Garmin (@Garmin) July 23, 2020
WastedLocker
If Garmin does turn out to be a victim of the WastedLocker ransomware, it won’t be alone as this new strain of ransomware has been spotted in the wild since May.
Spread by the villainously named Evil Corp group, WastedLocker is typically used to target large US companies, attempting to lock their files and demand huge ransoms of up to $14 million in bitcoin.
The ransomware attack begins with delivery of a malicious zip file called SocGholish which Symantec found is hosted on over 150 legitimate websites – including major US news sites – that had been compromised.
Inside SocGholish is a piece of JavaScript that pretends to be a browser update. This gathers information about the host system before dropping another malicious program that connects with a command and control domain.
The attackers then work to escalate privileges, disable Windows Defender, stop all services, and start encrypting files.
Symantec’s research team said the group behind WastedLocker were “capable of penetrating some of the most well-protected corporations”.
“As such, WastedLocker is a highly dangerous piece of ransomware,” Symantec said.
“A successful attack could cripple the victim’s network, leading to significant disruption to their operations and a costly clean-up operation.”
Unlike some ransomware groups, there is no evidence that Evil Corp uses WastedLocker to exfiltrate data for further extortion, sale, or secondary attacks.
Update: Garmin has confirmed reports that it suffered from a ransomware attack. In a statement, Garmin said it was "the victim of a cyber attack that encrypted some of [its] systems" and that no customer data or payment information has been exfiltrated.
Bleeping Computer verified Garmin was locked down by the WastedLocker ransomware through conversations with employees, screenshots of the encrypted files, and analysis of a virus sample.










