The world’s largest currency exchange has been offline for more than two weeks following a ransomware attack, with hackers demanding a ransom to restore the systems and return customer data.
Travelex called in cybersecurity experts at the start of the year in an effort to contain a malware attack which has kept its systems offline since New Year’s Eve.
Travelex stores have since been forced to conduct services manually, and banks around the world that rely on the company to supply money in foreign currencies have also been impacted, including Westpac.
Travelex customers using pre-loaded cards for foreign currency payments have also been left stranded and unable to access their money due to the ransomware attack.
In a new statement posted on the Travelex Canada website last week, the company admitted that it had been the victim of the ransomware known as Sodinokibi or REvil.
Sodinokibi is a ransomware software which encrypts files on victims’ networks and demands a ransom in exchange for them being decrypted.
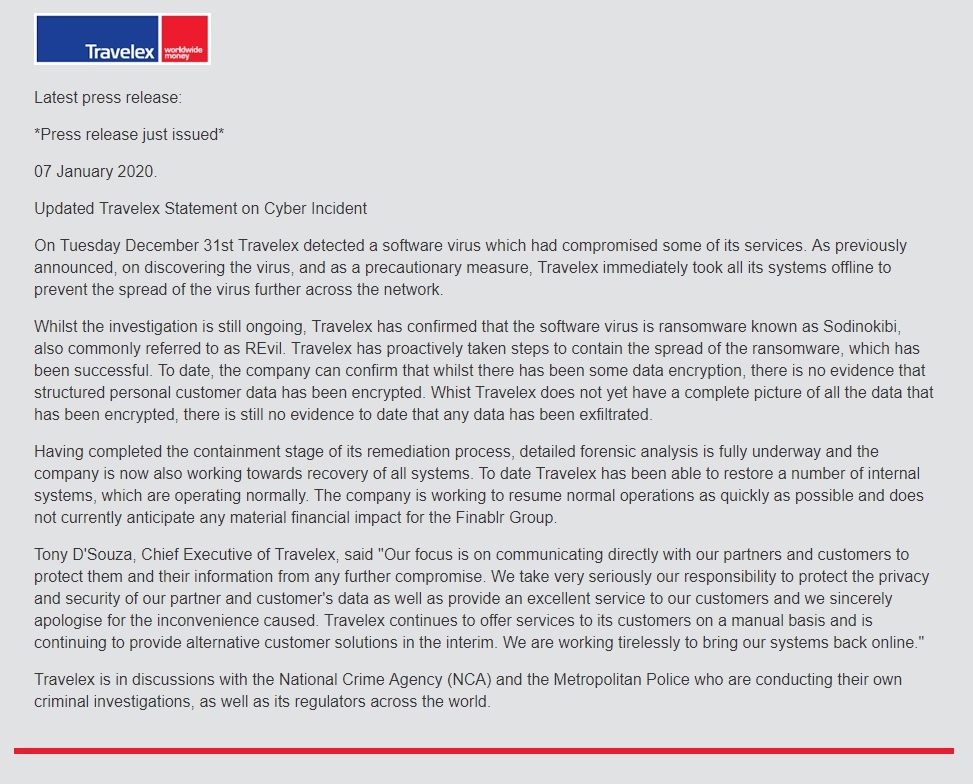
The statement on the Travel Canada website (www.travelex.ca).
It has been reported that the hackers have demanded a ransom of more than $8.5 million (4.6 million pounds) in exchange for the decryption of 5GB of customer data, including dates of birth, credit card information and national insurance numbers, along with the restoration of the company’s IT systems.
If the ransom is not paid, the hackers have said they will delete the Travelex computer systems and the data will be sold online.
But in the statement, Travelex didn’t mention the ransom and said there is “still no evidence to date that any data has been exfiltrated”, adding that some internal systems have already been restored.
“Travelex has proactively taken steps to contain the spread of the ransomware, which has been successful,” the press release said.
“To date, the company can confirm that whilst there has been some data encryption, there is no evidence that structured personal customer data has been encrypted.”
Travelex is also in discussion with the National Crime Agency and the Metropolitan Police over the criminal investigation, and a number of regulators around the world.
Travelex staff have also reportedly had to hand over their laptops as the company looks to stop the spread of the malicious software.
Travelex is working “tirelessly” to bring its systems back online, its chief executive Tony D’Souza said.
“Our focus is on communicating directly with our partners and customers to protect them and their information from any further compromise,” D’Souza said.
“We take very seriously our responsibility to protect the privacy and security of our partner and customer’s data as well as provide an excellent service to our customers and we sincerely apologise for the inconvenience caused.
“Travelex continues to offer services to its customers on a manual basis and is continuing to provide alternative customer solutions in the interim.”
The group behind the cyber attack has claimed to have had access to Travelex data for the last six months.
In a readme file, the hackers instructed Travelex to pay the ransom via bitcoin.
“It is just business,” the file said. “We absolutely do not care about you or your details, except getting benefits. If we do not do our work and liabilities - nobody will not cooperate with us. It is not in our interests.
“If you do not cooperate with our service - for us it does not matter. But you will lose your time and your data, cause just we have the private key. In practice time is much more valuable than money.”
Travelex is yet to confirm the date of when it expects the systems to be back online around the world, or whether it intends to pay the ransom.










