Apple has confirmed granting Australian law enforcement access to user notification data for the first time, which can identify a target's device and potentially intercept or recover text from notifications.
A transparency report Apple updated in recent weeks said 762 law enforcement applications for user data originated from Australia between January and June 2025, with four push token identifiers sought across two of the requests.
Apple granted one of the push token requests, and knocked back the other.
The company did not respond to a request for comment when Information Age sought the offence type that the tokens were used to investigate, and the types of information authorities were able to glean from them.
The requests “generally seek identifying details of the Apple account associated with the device’s push token, such as name, physical address and email address”, according to Apple's report.
It does not address if the requests covered the content data that apps also send to the Apple Push Notification (APN) service, called “notification payloads”, which include the actual text displayed.
However, neither APN or Google’s Android push notification service require apps to end-to-end encrypt the notification payload.
Since adding the push token category to its biannual breakdown of user data disclosures less than four years ago, Apple has complied with 958 of 1408 requests for 4,462 push tokens globally.
Google does not include a category for push tokens in its reports.
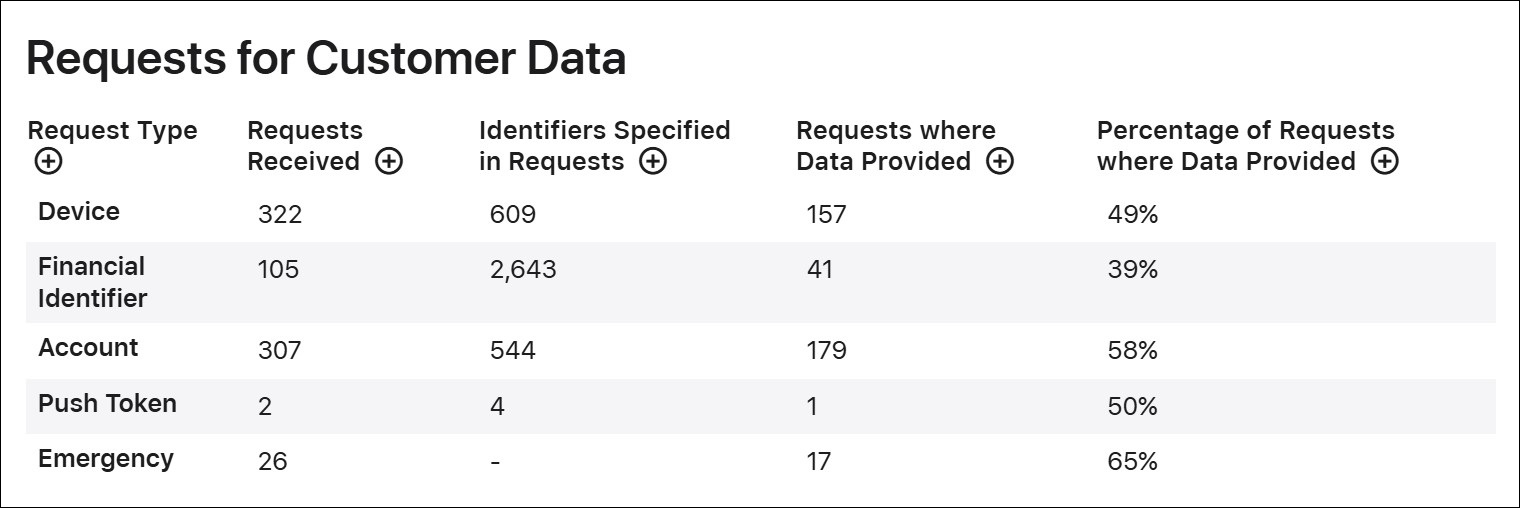
Government requests for customer data in Australia, January to June 2025. Image: Apple
Deleted messages extracted from push notifications
Last week the FBI revealed that when it has physical access to an iPhone, it can extract deleted incoming Signal messages from the device’s notifications log even when the messages and app have been deleted.
The capability was revealed in evidence admitted during a trial of nine Antifa protesters who were found guilty of a mix of convictions for their roles in a non-fatal shooting of a police officer, and rioting outside a Texas Immigration and Customs Enforcement (ICE) facility.
Supporters of the group who attended the trial published a summary of the exhibit and shared it with 404Media, which broke the story.
Some apps leak both the non-content data used to deliver notifications like account name and user ID, as well as the notifications’ plaintext – including apps that market themselves as end-to-end encrypted.
A 2024 peer-reviewed study comparing the information that apps leak when sending notification data to Android devices found Skype, Discord, and WeChat shared “personal message content” with Firebase Cloud Messaging – Google’s push token delivery service.
Although this implies a hypothetical capability to remotely recover deleted content, the only publicly disclosed examples of the information that agencies have gleaned from remote access to notification data involve using push token’s non-content data for identity linkage, such as tying pseudonymous app accounts to devices, IP addresses, and subscriber records.
New York police have previously obtained a dual-factor authentication push token from communication app Talkatone and used it to ask Apple which iCloud account was linked to it. Apple returned iCloud information for one of two suspects later charged in the killing of a food delivery driver.
In a search warrant application, the US Bureau of Alcohol, Tobacco, Firearms, and Explosives sought Snapchat records linking a target account to device-related identifiers including push tokens, Android ID, Apple ID, and other device identifiers.
The FBI got Google to provide IP addresses and the names of six accounts linked to a push token that encrypted messaging app TeleGuard provided; one of those accounts included the name of a suspect who was later charged with child abuse.
However, the handful of court documents are not a reliable sample size to extrapolate how notification data is leveraged.
Safer default: turn off previews
Turning off message previews is the simplest way to reduce the risk of notification text being recovered.
If notifications are set to show only the app name — and no sender or message text at all — less plaintext is exposed to push-delivery systems and the phone’s notification history.
It is a stronger safeguard against what push services and a seized device can reveal, than against what an app developer may still hold on its own servers.
Many major app owners do not cover push tokens in their transparency reports.
This means there is no way of knowing how many such requests were included in customer data applications Australian government agencies made in the 2024-25 financial year to Meta, Google, Snap, or TikTok.










