Internet giants Google and Cloudflare have warned the encryption standards underpinning modern digital security may be broken by quantum machines sooner than expected.
Google previously issued a call to action in February when it warned the “digital locks” protecting “bank transfers, private chats, trade secrets” and “classified information” could “easily be broken” in coming years.
Such an event has long been described as “Q-Day” – a turning point when ‘Cryptographically Relevant Quantum Computers’ (CRQC) are able to solve the complex logic behind public-key encryption standards.
Although security experts have long estimated such a date could arrive in the mid-2030s, both Google and Cloudflare have now officially set deadlines for their own post-quantum cryptography (PQC) migrations to 2029.
“This new timeline reflects migration needs for the PQC era in light of progress on quantum computing hardware development, quantum error correction, and quantum factoring resource estimates,” Google security experts wrote in late March.
“It’s our responsibility to lead by example and share an ambitious timeline.”
Information Age understands that, among other measures, Google's multi-year migration will involve securing its infrastructure and rolling out further “post-quantum capabilities” across its products.
Notably, the company said it would test PQC enhancements in the next Android 17 beta, followed by general availability in the operating system’s eventual production release.
“Android is swapping today’s digital locks for advanced encryption to help enhance the security of every app you download — no matter how powerful future supercomputers get,” read a Google security blog.
The company has also updated its threat models to prioritise PQC migration for authentication services.
“We recommend that other engineering teams follow suit,” Google wrote.
Cloudflare joins quantum deadline
Networking giant Cloudflare announced on Tuesday that it would also expedite its “internal Q-Day readiness timeline” to 2029.
Though Cloudflare already enabled post-quantum encryption for all websites and application programming interfaces (APIs) in 2022, the company said “credible new research” and “rapid industry developments” suggested the deadline to be fully post-quantum secure was “much sooner than expected”.
Further to Google’s research, Cloudflare cited a breakthrough from quantum computing company Oratomic that estimated ‘P-256’ cryptography could be broken with a “shockingly low” 10,000 quantum bits.
Notably, just six months after Australia’s Minister for Defence Richard Marles warned that Australian companies needed to prepare for powerful quantum computers, Cloudflare speculated those pursuing the technology would soon not disclose their progress.
“Indeed, there is ample reason to expect that progress will leave the public eye,” Cloudflare researcher Bas Westerbaan wrote.

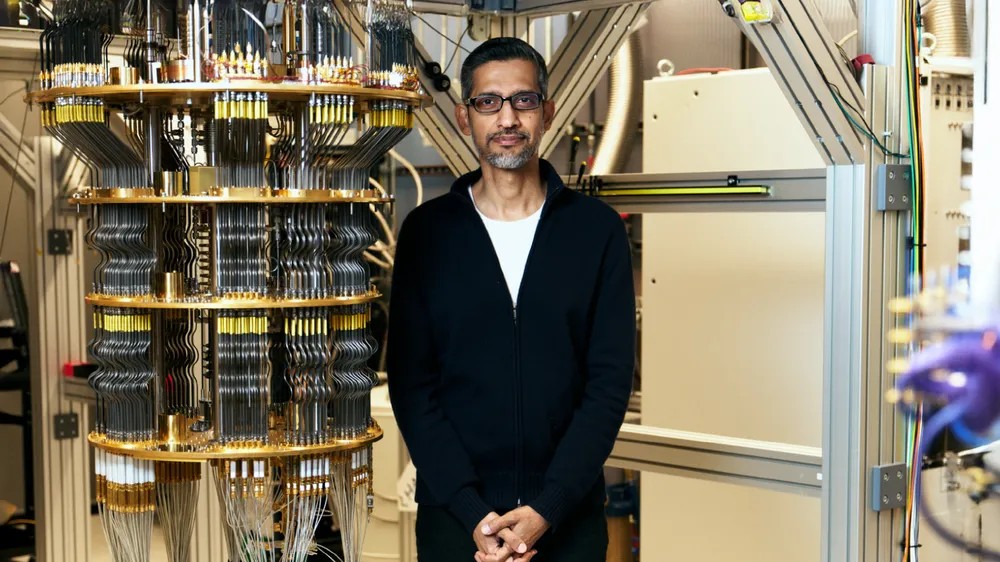
'Q-Day' could be upon us before the end of the decade, Google and Cloudflare say. Image: Shutterstock
Cracking blockchain may not be as hard as expected
In a Google whitepaper released last week, researchers at the company’s Quantum AI Lab found future quantum computers could solve the elliptic curve cryptography (ECC) that protects blockchain technologies such as cryptocurrency with fewer resources than previously realised.
Specifically, the research estimated the ‘ECDLP-256’ logarithm underpinning ECC could be cracked “in a few minutes”, using approximately 20 times less physical quantum bits than previously thought.
The research also showed decryption could be performed with fewer ‘Toffoli gates’ – an expensive facet of quantum computing that helps determine how much time is needed to execute algorithms.
Given ECC is widely used to secure the internet, Google approached the United States government and developed a “new method” to describe the vulnerabilities using a “zero-knowledge proof”.
“[We did this] so they can be verified without providing a roadmap for bad actors,” researchers wrote.
“We urge other research teams to do the same to keep people safe.”
Hackers aren’t waiting
Google also warned that “malicious actors” were likely already preparing for attacks using “store now, decrypt later” techniques.
Such tactics allow threat actors – including nation states, insiders, ransomware collectives, and others – to download and store current, encrypted data or ‘ciphertexts’ with the intention of decrypting them once quantum computers are available.
“This store-now-decrypt-later attack is the main motivator behind the current adoption of post-quantum cryptography,” wrote Google engineers.
“We need to implement the quantum-safe algorithms now.”
Meanwhile, tech giant IBM has adopted a Sydney researcher’s blueprint for quantum computing error correction as part of the company’s ambitions to build the first large-scale, fault-tolerant quantum computer by 2029.